New RTF macro Malware from the Dridex gang
March 23, 2016
In the aftermath of Locky many companies started blocking EXE files directly attached or in ZIP files on their mail gateways. Some moved further and started removing active content in DOC, XLS, and other MS Office files. Today an old file type got used again and the virus scanner hit rate was really bad again.
Details
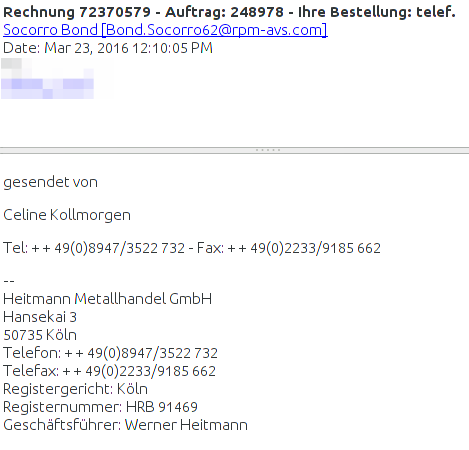
The Malware gets delivered by mails with a RTF file attached (which is often used in the medical area), which e.g. looks like this:
The company exists if you check before opening the attachment. Normally bad RTF files did contain EXE files within them, but not this time. This time it contains highly obfuscated macro code, which MS Word executes. which looks like this:
Sub Document_Open()
Dim HGFDSXDSFVV
HCFDSFDSFB = "hel"
VDSFCDSJ = "qweee"
GoTo PQOycAsH
Dim XJwoBhgN As String
Open "JQJLAG.ANU" For Binary As 66
GoTo pKlIahvf
Dim wVyQZrAv As String
Open "CTTBNH.FEB" For Binary As 18
Put #18, , wVyQZrAv
Close #18
pKlIahvf:
Put #66, , XJwoBhgN
...
which then did use WScript.exe to download a file from
http://wrkstn09.PEORIASENIORBAND.COM/dana/home.php
other researchers report followingURLs:
http://connect.businesshelpa-z.com/dana/home.php
http://wrkstn09.satbootcampaz.com/dana/home.php
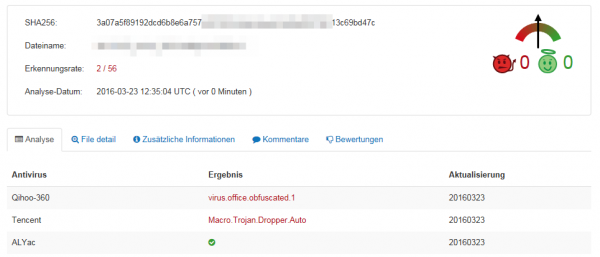
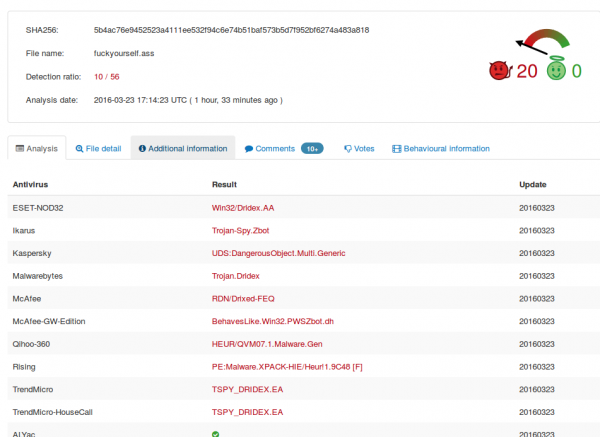
The file is called fuckyourself.ass which is in reality a EXE file, which contains the Malware itself. Uploading this (we’re one of the first it seems 😉 ) to Virustotal showed that only 2 virus scanner detected the Malware:
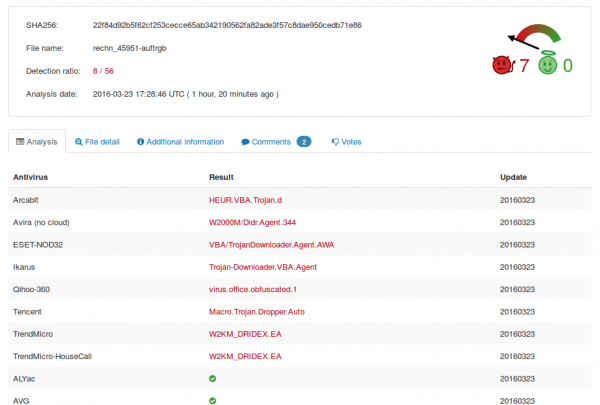
Some hours later and after others saw the file also in the wild and as we reported the file to virus vendors it looks a little bit better, but not good – for the dropper 8/56:
and for the malware itself 10/56:
I normally don’t write about single viruses, but this one is a show case for some opinions I’ve for some time now.
- Forget about normal virus detections – sure keep it on Windows system but don’t count on it.
- You really need to implemented procedures as described in this early blog post.
- It gets more and more important to implement a sand-boxing technology, where all your files which get to you’re company from the internet gets executed / opened. And this means every file .. not only executables. There are also sand boxing technologies that run on premise or in an European data center.
- Bigger companies can mitigate that problem easier, the problem child are home users and small companies.
I don’t have a good solutions for home users so far … maybe someone knows something that I could recommend the Windows home users I know.
Blue Code mobile payment – All show and no substance [3. Update]
March 20, 2016
[Update]
The vendor contacted me and told me they are working on a fix right now, which should be released shortly. I also got contacted by 3rd parties and they asked if the whole system is broken or not. To make it clear for the non experts. My findings are “easily” fixable and I can’t say anything about the whole system as I didn’t look at it. The vendor has fixed following 2 problems
- bad HTTPS setup for the webservice
- client certificates length (now RSA2048).
[/Update]
Shopping in my local super market I saw an other customer paying with a barcode on the display of his mobile. Looking a little bit around I saw also the ad for it. The service/product is called Blue Code and is from a local company Secure Payment Technologies GmbH based in Innsbruck and is used by some big retail stores.
As you know me, I like to know how stuff around me works and how secure they are. Searching around a little bit in the Internet I didn’t find anything above marketing stuff on how the system works. This intrigued me, as not documented normally means there are some skeletons in the closet. So this post is about the my look into the system.
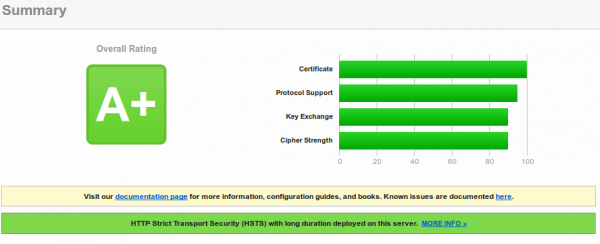
I normally start with the basics. In this case checking the HTTPS stuff and taking a look at the Android App. Both are done without installing the App on one of my devices.
First Look
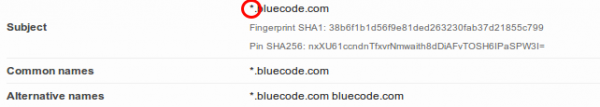
Looks good, but I saw something additional:
Yes, that’s a wild card certificate. So even if they have an other more secure TLS setup for the payment stuff this certificate would be valid for it. That’s bad security practise. But maybe they use an other domain for the payment stuff or do certificate pinning. So I downloaded the APK. Use this nice site to download the Blue Code APK on your desktop for analysing. APK files are just ZIP files with a special structure, so I’ve extracted the files and took a look at the strings. I took a look at the last 3 versions which I could download.
I found something interesting in the Blue Code_v1.2.0_apkpure.com.apk (the oldest of the three) …
$ strings classes.dex | grep http
[Copyright (c) 2000-2014 The Legion of the Bouncy Castle Inc. (http://www.bouncycastle.org)
...
#http://202.4.114.227:8080/merchants
...
https://sdk.hockeyapp.net/
https://support.bluecode.com/a/
The Bouncy Castle is a crypto library for Java in this case and HockeyApp is for a platform for application development. The IP address is more interesting, it belongs to an ISP from Bangladesh. Hey? The company is from Tirol / Austria – outsourced development? The Blue Code_v1.3.1_apkpure.com.apk and Blue Code_v1.3.2_apkpure.com.apk does not contain that string. Also the crypto lib seems to be changed. Anyway the host was not reachable from my computer so I think that’s legacy host that got removed.
So far it seems no other domains are in the App. A search for sub domains shows following:
$ strings resources.arsc | grep bluecode.com
...
https://www.bluecode.com/login
mobile-ca.bluecode.com
mobile-api.bluecode.com
...
Oh, that TLS setup looks not that good:
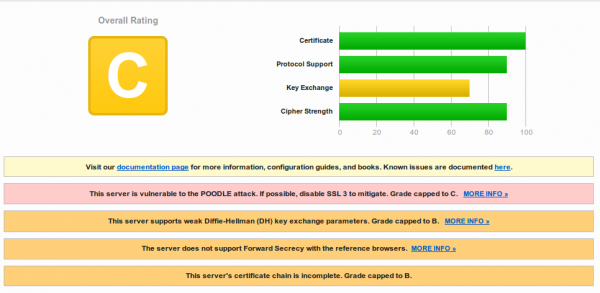 hm .. lets take a look at the certificate …. oh … its the same:
hm .. lets take a look at the certificate …. oh … its the same:
So different servers use the same wild card cert … that’s really “good” security practise :-). Are TLS certs too expensive? https://mobile-api.bluecode.com uses also the same certificate and the same TLS setup as https://mobile-ca.bluecode.com (run on the same IP address).
Both hosts look like web services … so I guess the App talks with them, which means the website has a better security than the payment web services? I should look deeper into it.
Note the vendor: Certificate pinning helps only if you don’t use the same wild card certificate for all services, this way if you’re web server gets compromised an attacker can use that for fake your payment webservices.
The setup for a deeper look
Now it is time to look at the traffic the App generates while talking to its servers. Looking at the files packed into the apk file I saw that under /res/raw/ multiple CA certificates (including the CA for the web site and service certificate) got shipped. So I’ll guess there is some certificates pinning done.
So I got my old Nexus 7 out from a storage drawer, and did following to it:
- Unlock Bootloader
- Factory restore with Android 5.1.1
- Rooted it
- Installed Xposed Framework
- Installed JustTrustMe and SSLUnpinnig Modules for Xposed
After that I installed Burp and configured it as an HTTPS proxy on my PC. I’ve already shown how to do that in this blog post. After that I needed only to do following on the tablet:
- configure Burp as the proxy for the Wifi connection
- install the the Burp CA on the tablet
- download and install the BlueCode App.
First launch of the App
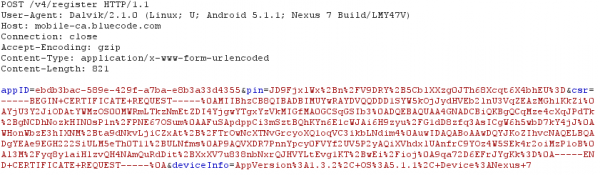
At first launch you need to provide a PIN code for something – it was not for what I first thought, but more about that later. After entering you PIN twice the App starts talking with the server.
The two requests to
https://www.bluecode.com/json/support_mobile_app_pages.jsonandhttps://www.bluecode.com/json/support_mobile_allgemein.json
return only some text for the App. But the next request is more interesting, it is a certificate signing request (CSR):
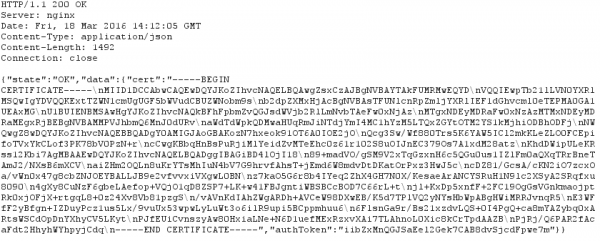
And there is also a parameter “pin” in the request (salted hash?). Looking at the CSR it seems to be a little short. Anyway the response from the server is a certificate.
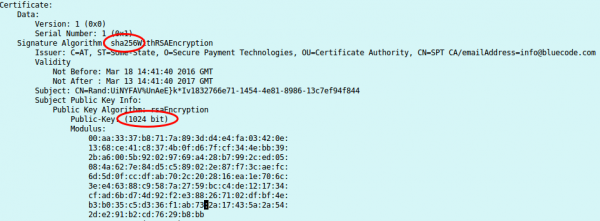
Taking a look at that certificate shows following:
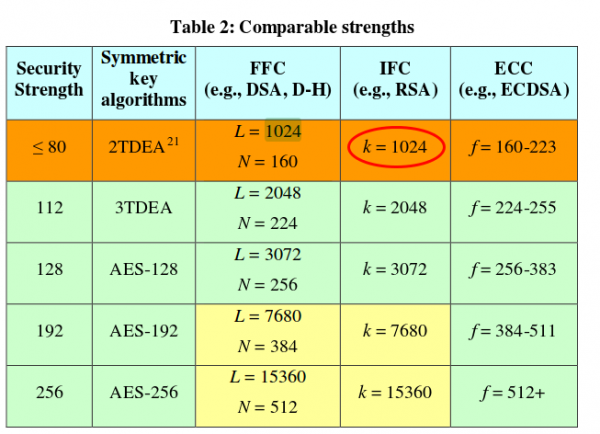
I know now why it looked that short, its a 1024 RSA certificate, but signed with SHA256. Someone didn’t understand crypto here. Signing an RSA1024 Key with SHA256, does not make any sense. If you won’t believe me take a look what NIST(National Institute of Standards and Technology) says. From the PDF:
RSA 1024 has a security of lower than 80bit and should not be used for years now!!!
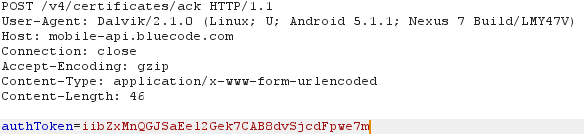
After this request, the next request gets send to mobile-api, with the authToken the App got from the previous request.
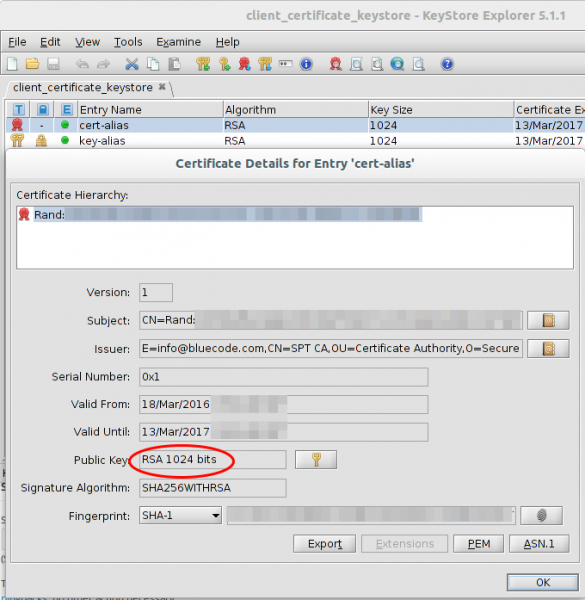
This request fails with the HTTPS proxy as the App makes a TLS client authentication, for which my proxy does not have the private key. After some short searching I found it under: /data/data/com.spt.bluecode/app_Certificates/client_certificate_keystore
I copied the file to my computer and tried to open it … I “just” need to get the private key now.
Lets stop with looking into the security of Blue Code for mow, as the weekend is almost over and the weather was really good and I needed to go ski montaineering also. But maybe I’ll look later deeper into the system …. So far I found following security problems:
- bad HTTPS setup for the webservice
- wildcard certificates used over multiple servers/services
- client certificates length (RSA 1024bit) which should not be used for years
So many security problems after looking at it only for some hours does not bode well ….
[Update]
It seems the software has a check that should detect if a devices is rooted …. does not seem to work in my case, maybe I don’t have that directories on my system … 😉
[\Update]
ps: Has someone of you documentation on the protocol of Blue Code? This would allow a high level check and theoretical security check without looking at the traffic.
Block Ransomware botnet C&C traffic with a Mikrotik router
March 14, 2016
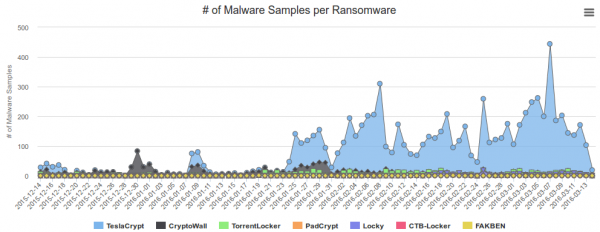
In my last blog post I wrote about blocking, detecting and mitigating the Locky Ransomware. I’ve referenced to a earlier blog post of mine which allows to block traffic to/from the Tor network. This blog post combines both – a way to block Ransomware botnet C&C traffic on a Mikrotik router. The base are the block lists from Abuse.ch, which also provide a nice statistic. Locky is not the most common Ransomware today.
Linux part
You need also a small Linux/Unix server to help. This server needs to be trustworthy one as the router executes a script this server generates. This is required as RouterOS is only able to parse text files up to 4096 by itself, and the IP address and domain list is longer.
So first we create the script /usr/local/sbin/generateMalwareBlockScripts.py on the Linux server by downloading following Python script. Open the file and change the paths to your liking. The filename path works on CentOS, on Ubuntu you need to remove the html directory. Now make the file executable
chmod 755 /usr/local/sbin/generateMalwareBlockScripts.py
and execute it
/usr/local/sbin/generateMalwareBlockScripts.py
No output is good. Make sure that the file is reachable via HTTP (e.g. install httpd on CentOS) from the router. If everything works make sure that the script is called once every hour to update the list. e.g. place a symlink in /etc/cron.hourly:
ln -s /usr/local/sbin/generateMalwareBlockScripts.py /etc/cron.hourly/generateMalwareBlockScripts.py
Mikrotik part
Copy and paste following to get the IP address script onto the router:
/system script
add name=scriptUpdateMalwareIPs owner=admin policy=ftp,reboot,read,write,policy,test,password,sniff,sensitive source="# Script which will download a script which adds the malware IP addresses to an address-list\
\n# Using a script to add this is required as RouterOS can only parse 4096 byte files, and the list is longer\
\n# Written by Robert Penz <[email protected]> \
\n# Released under GPL version 3\
\n\
\n# get the \"add script\"\
\n/tool fetch url=\"http://10.xxx.xxx.xxx/addMalwareIPs.rsc\" mode=http\
\n:log info \"Downloaded addMalwareIPs.rsc\"\
\n\
\n# remove the old entries\
\n/ip firewall address-list remove [/ip firewall address-list find list=addressListMalware]\
\n\
\n# import the new entries\
\n/import file-name=addMalwareIPs.rsc\
\n:log info \"Removed old IP addresses and added new ones\"\
\n"
and copy and paste following for the DNS filtering script – surely you can combine them … I let them separated as maybe someone needs only one part:
/system script
add name=scriptUpdateMalwareDomains owner=admin policy=ftp,reboot,read,write,policy,test,password,sniff,sensitive source="# Script which will download a script which adds the malware domains as static DNS entry\
\n# Using a script to add this is required as RouterOS can only parse 4096 byte files, and the list is longer\
\n# Written by Robert Penz <[email protected]> \
\n# Released under GPL version 3\
\n\
\n# get the \"add script\"\
\n/tool fetch url=\"http://10.xxx.xxx.xxx/addMalwareDomains.rsc\" mode=http\
\n:log info \"Downloaded addMalwareDomains.rsc\"\
\n\
\n# remove the old entries\
\n/ip dns static remove [/ip dns static find comment~\"addMalwareDomains\"]\
\n\
\n# import the new entries\
\n/import file-name=addMalwareDomains.rsc\
\n:log info \"Removed old domains and added new ones\"\
\n"
To make the first try run use following command
/system script run scriptUpdateMalwareIPs
and
/system script run scriptUpdateMalwareDomains
if you didn’t get an error
/ip firewall address-list print
and
/ip dns static print
should show many entries. Now you only need to run the script once a hour which following command does:
/system scheduler add interval=1h name=schedulerUpdateMalwareIPs on-event=scriptUpdateMalwareIPs start-date=nov/30/2014 start-time=00:05:00
and
/system scheduler add interval=1h name=schedulerUpdateMalwareDomains on-event=scriptUpdateMalwareDomains start-date=nov/30/2014 start-time=00:10:00
You can use the address list and DNS blacklist now in various ways .. the simplest is following
/ip firewall filter
add chain=forward comment="just the answer packets --> pass" connection-state=established
add chain=forward comment="just the answer packets --> pass" connection-state=related
add action=reject chain=forward comment="no Traffic to malware IP addresses" dst-address-list=addressListMalware log=yes log-prefix=malwareIP out-interface=pppoeDslInternet
add action=reject chain=forward comment="report Traffic to DNS fake IP address" dst-address=10.255.255.255 log=yes log-prefix=malwareDNS out-interface=pppoeDslInternet
add chain=forward comment="everything from internal is ok --> pass" in-interface=InternalInterface
If a clients generates traffic to such DNS names or IP address you’ll get following in your log (and the traffic gets blocked):
20:07:16 firewall,info malwareIP forward: in:xxx out:pppoeDslInternet, src-mac xx:xx:xx:xx:xx:xx, proto ICMP (type 8, code 0), 10.xxx.xxx.xxx->104.xxx.xxx.xxx, len 84
or
20:09:34 firewall,info malwareDNS forward: in:xxx out:pppoeDslInternet, src-mac xx:xx:xx:xx:xx:xx, proto ICMP (type 8, code 0), 10.xxx.xxx.xxx ->10.255.255.255, len 84
ps: The Python script is done in a way that it easily allows you to add also other block lists … e.g. I added the Feodo blocklist from Abuse.ch.
Powered by WordPress
Entries and comments feeds.
Valid XHTML and CSS.
33 queries. 0.063 seconds.