Damn it! Patch your DNS Server!
July 26, 2008
In the last days an exploit has been released, but still many big companies have not patched their recursive DNS server. According to the Austrian CERT which released a report two third of the recursive DNS are still not patched. These are not small companies or system, according to The Register the big US ISPs like AT&T, BT and Time Warner as Bell Canada are not patched. There are even some hints that attacks are already carried out.
So Damn it! Patch your DNS servers, you’re risking the security of your customers!
Even Microsoft released following security warning Increased Threat for DNS Spoofing Vulnerability which tells you to install the patch MS08-037 at once. But what do you think can be even worse?
Apple
They have still not provided a patch for OS-X-Server, that just shows that apple can’t be taken serious in the server world.
And I wondered why Ubuntu did no upgrade of MaraDNS
July 22, 2008
In the last weeks all major DNS vendors and distributions did upgrade their DNS servers, but I was not getting an update for the DNS server which I use: MaraDNS
So I did take a look around and found following blog posting by the MaraDNS guys: MaraDNS is immune to the new cache poisoning attack. Which basically explains that because of DJB (whose DNS server I used before it was removed from Ubuntu Hardy) they use query ID and source port randomization since the first public release. Good that I always search for a secure implantation of a service I need. Why are so many people still using bind that much. It can’t be that every setup needs features which only bind provides. It must be laziness or they don’t care about security.
Lynis – an auditing tool for Linux/Unix
July 19, 2008
The first step to higher security of your system is to assess the current state of the system. Lynis is a small command line tool, licensed under GPL 3, which can help you achieving this. From the authors homepage:
Lynis is an auditing tool for Unix (specialists). It scans the system and available software, to detect security issues. Beside security related information it will also scan for general system information, installed packages and configuration mistakes.
This software aims in assisting automated auditing, software patch management, vulnerability and malware scanning of Unix based systems. It can be run without prior installation, so inclusion on read only storage is no problem (USB stick, cd/dvd).
He also clearly states what Lynis is not:
Not a hardening tool: Lynis does not fix things automatically, it reports only (and makes suggestions).
More to the technicial stuff: The basis of the program are shell scripts which scan the operating system and installed software (e.g. old software) but also stuff like SSL certificates (e.g. expire date). The software checks for accounts without password or wrong file permissions and it takes also a look at your local firewall. It runs under many Linux and Unix versions including Debian and Ubuntu.
“Transparent end-to-end encryption for the Internets” is not the solution
July 13, 2008
Last week the guys behind the popular torrent site The Pirate Bay went public with their project of an opportunistic encryption of all traffic from an computer. The project is called “Transparent end-to-end encryption for the Internets” (IPETEE) but it is not the first time something like this is tried. Due to the pressure by the media industry it has more success chances than the last tries but I think we should target something else.
So what should be our target?
To build an overlay network with allows anonymous, encrypted and censor resident communication for unchanged IP based protocols over the internet. From the user perspective the software creates a virtual network adapter like OpenVPN does and every traffic that goes into that device is send via this overlay network. The overlay network does not send the traffic to the other peer directly (in this case the communication would not be anonymous) but via other peers taking part in that network. The more security you need to more peers it takes, but it will also get slower. This enables the usage of the network by different user groups.
This would be a real solution and not a half one like the idea from The Pirate Bay guys. Ah, before I forget it, following are non-goals.
- This network should not guard against information leak through programs which use this network (e.g. mail client sending real IP address)
- No military security/anonymity is targeted, it should be just enough to have a plausible deniability.
- It is not the goal of this network to provide access through the network to the outside world. What goes into to network should stay there. But this does not mean that any effort is invested to prevent anyone to play proxy. (e.g. http proxy)
What do you think about it?
Kpartx: a tool for mounting partitions within an image file
July 12, 2008
Kpartx can be used to set up device mappings for the partitions of any partitioned block device. It is part of the Linux multipath-tools. With kpartx -l imagefile you get an overview of the partitions in the image file and with kpartx -a imagefile the partitions will accessible via /dev/mapper/loop0pX (X is the number of the partition). You can mount it now with mount /dev/mapper/loop0pX /mnt/ -o loop,ro. After unmounting you can disconnect the mapper devices with kpartx -d imagefile.
There are packages for Debian and Ubuntu.
- Ubuntu: http://packages.ubuntu.com/de/hardy/kpartx
- Debian: http://packages.debian.org/search?keywords=kpartx
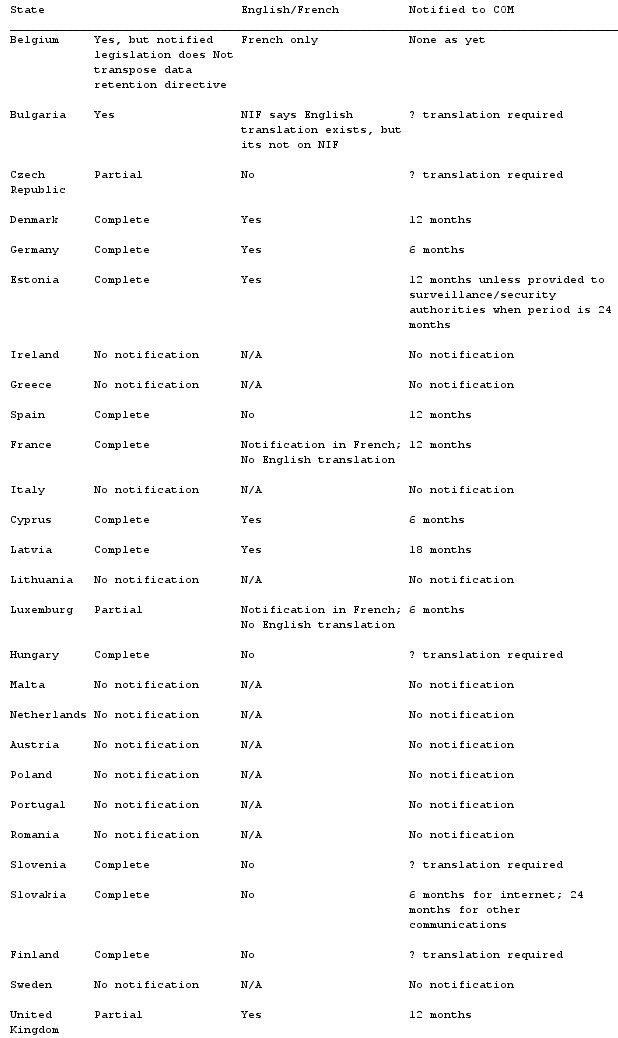
EU Member States Data Retention Transposition Measures
I got my hand on this list which is out of a PDF from the European commission, and I though it maybe also interests others. It shows the status of data retentions laws in the EU member states. So here is the list. (The list is sorted by the native names of the nations and not the English ones I used here, e.g. Deutschland vs Germany)
.
Fix for Kopete 0.12.7 to work again with ICQ
July 2, 2008
Yesterday my Kopete stopped working with the ICQ network. The ICQ told me that my client version is too old. Here is the fix to make it work again. Look in the ~/.kde/share/config/kopeterc file and change the values of the variables to following (which are from trunk):
[ICQVersion]
Build=0x17AB
ClientId=0x010A
ClientString=ICQ Client
Country=us
Lang=en
Major=0x0006
Minor=0x0000
Other=0x00007535
Point=0x0000
After a restart of Kopete everthing works again for me.
Powered by WordPress
Entries and comments feeds.
Valid XHTML and CSS.
26 queries. 0.051 seconds.





