Howto to quick test a DSCP based QoS system?
August 29, 2013
You’ve just completed your QoS system, which is based on DSCP for classifying and managing network traffic? Sure there are many sophisticated methods to validate your configuration, but there is also a really simple one which you can do from every Windows or Linux PC as a first check.
And you won’t believe it – the program is called ping. On Linux use the option -Q to set the DSCP value of the packets. From the manual:
-Q tos Set Quality of Service -related bits in ICMP datagrams. tos can be either decimal or hex number. Traditionally (RFC1349), these have been interpreted as: 0 for reserved (currently being redefined as congestion control), 1-4 for Type of Service and 5-7 for Precedence. Possible settings for Type of Service are: minimal cost: 0x02, reliability: 0x04, throughput: 0x08, low delay: 0x10. Multiple TOS bits should not be set simultaneously. Possible settings for special Precedence range from priority (0x20) to net control (0xe0). You must be root (CAP_NET_ADMIN capability) to use Critical or higher precedence value. You cannot set bit 0x01 (reserved) unless ECN has been enabled in the kernel. In RFC2474, these fields has been redefined as 8-bit Differentiated Services (DS), consisting of: bits 0-1 of separate data (ECN will be used, here), and bits 2-7 of Differentiated Services Codepoint (DSCP).
On Windows the same is achieved with -v
In both cases you need to provide the Type of Service (TOS) byte. While this is not the wished DSCP value, the ToS byte (or 8-bits) encompasses DSCP. DSCP only uses the first 6 bits of the ToS byte and ignores bits 7 and 8. You’re asking ??hey?? 😉
There is a quite easy way to get from one to the other: DSCP * 4 = TOS, or you can use following table.
Most VoIP systems use AF31(DSCP 26) for signaling (e.g. SIP) and EF (DSCP 46) for voice/media (e.g. RTP). This means for testing we use
ping -Q 104 <ip_address> # for DSCP 26
ping -Q 184 <ip_address> # for DSCP 46
After calling these commands you can easily check your counters if the increment correctly. After this put some load on the connection/link e.g. with FTP or SCP and let the ping run, it should be stable and with a low latency. If not the VoIP stuff with also not work. 😉
This quick test can also help you by an other problem. You need to deploy a system which relies on the fact that the DSCP value in not being stripped away in transit. For this you use the above command and let Wireshark run.
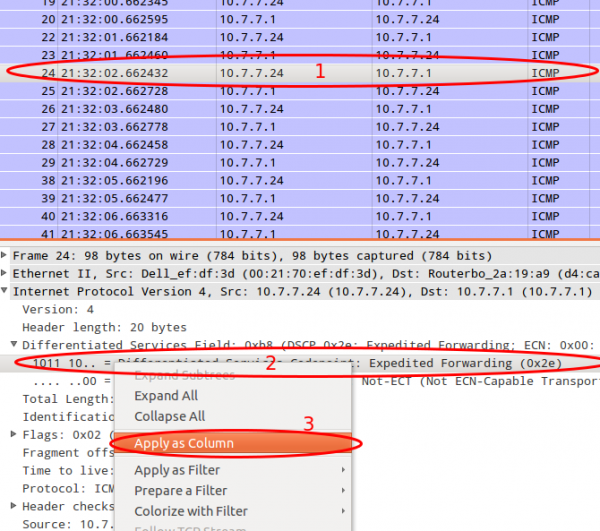
First you need to add the DSCP colum. Just select a packet and then select the DSCP header and use the right mouse button to get to the “Apply as Column” menu entry.
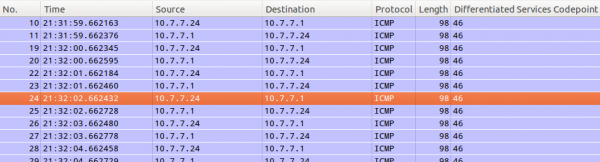
After this you can just look at the DSCP values. If they travel across the network everything is Ok.
Howto migrate mails from courier-imap without the passwords
August 26, 2013
I needed to move to a new mail server as the old one got too old. I had one problem – i didn’t know the old passwords of the virtual courier-imap users and the new system didn’t use the same hashing. It was ok to use new passwords for the new server, but as I needed to sync the most mails before I disabled the old mail server. This was needed as some users had really big mailboxes which would take too long to sync. So I needed a way to access the mails without knowing or reseting the old password. This post describes how I did the migration:
- I created a new user called “migrate” on the old mail server. I removed than its mail directory, in my case:
rm -rf /var/mail/domains/penz.name/migrate
And than I created a symlink to the mail of a user I wanted the mails to migrate:
ln -s /var/mail/domains/penz.name/robert/ /var/mail/domains/penz.name/migrate
Now I was able to login to the account with the “migrate” user and password - For the migration I used the defacto standard “imapsync”. I called it for the first user to check if it worked correctly. (checked also the mails on the new server and so on …)
- Now I wrote a small script which did create a symlink, started imapsync, removed the symlink, create a new symlink, …… sure with some error handling 😉
- All of the above was done without the user noticing. Most Mails where now migrated except the changes to the old mailboxes after imapsync did its job.
- I did send a mail to the users telling them of the move to the new server and providing them with the exact date of the change and their new login data, and that it could take some hours until all of there mails were migrated.
- At the given date I changed the DNS entries to the new server and stopped the SMTP/Webmail service on the old server and made sure the IMAP service was only reachable for the imapsync script (with iptables – localhost and uid check). The users which already got to the new mailserver (be it with Webmail or IMAP) got most of their mails – they others couldn’t connect until there dns server got the change. (It was done on a weekend)
- New mails from other SMTP servers where deferred or already delivered to the new server.
- After I made sure that the old mailboxes can’t be changed I started the script again and sync the differences to the server. This was now really fast as imapsync needed only to transfer a few mails.
- After the script was through I could switch the old server off.
I hope these steps help others – if you’ve an other/better way to migrate, tell me about it in the comments. Thx.
Powered by WordPress
Entries and comments feeds.
Valid XHTML and CSS.
30 queries. 0.123 seconds.





