Decoding SNMPv3 encrypted traffic in Wireshark
January 7, 2016
Talking with fellows about SNMPv3 I hear often that its not that critical that SNMP is encrypted and that encryption makes debugging more complicated as they can’t see what is send over the network.I won’t talk about the need for encrypting SNMP as it is like SSH gets used instead of Telnet. This post shows how easy it is to decode SNMPv3 encrypted messages with Wireshark (if you know the secrets 🙂 ). This is possible as SNMPv3 is a simple UDP protocol which encodes the packets with a shared secret and does not use forward secrecy like TLS does.
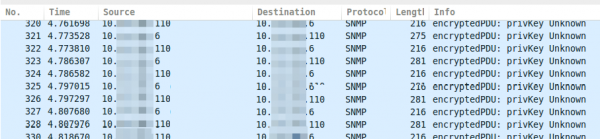
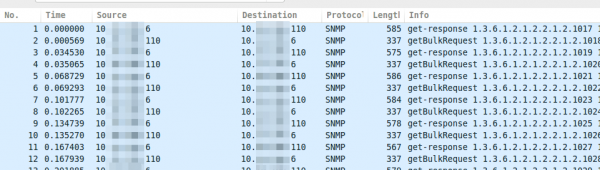
If you take a look on properly encrypted SNMPv3 traffic it looks like this.
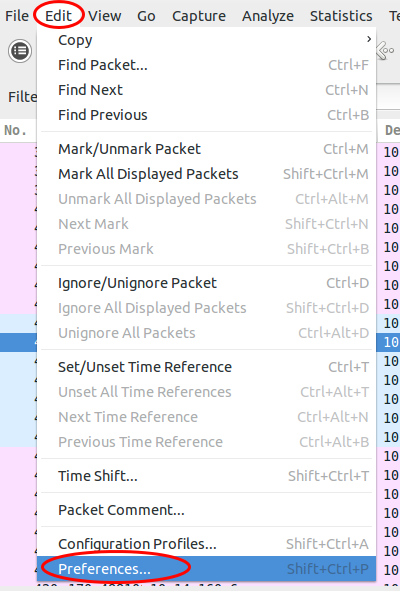
Now you just click on “Edit | Preferences”:
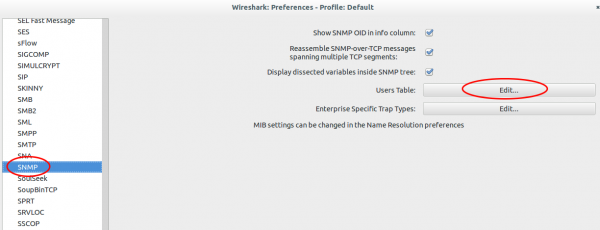
Search for “Protocols | SNMP” and click on “User Table | Edit”.
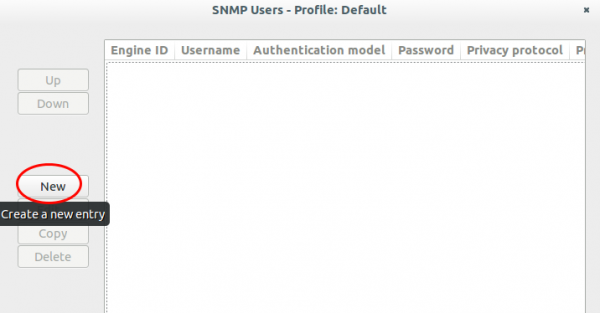
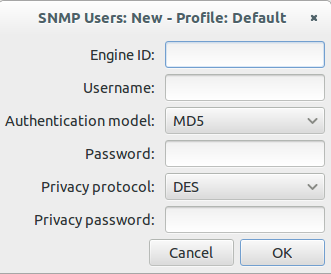
Click onto the “New” button:
Now enter your user name, select the authentication and encryption method and provide the 2 passwords. You don’t need to provide the Engine ID normally.
After clicking onto Ok multiple times the traffic looks like this:
If you use one SNMP profile for multiple systems its nice that the values get stored in the Wireshark preferences. Hope this takes some fear away from SNMPv3. 🙂
7 Comments »
RSS feed for comments on this post. TrackBack URI
Leave a comment
Powered by WordPress
Entries and comments feeds.
Valid XHTML and CSS.
39 queries. 0.075 seconds.






[…] want to look at encrypted SNMPv3 packets (Wireshark is able to decrypt it, if provided the […]
Pingback by Howto live-sniffer traffic on a remote Linux system with Wireshark | Robert Penz Blog — October 2, 2016 #
Very good brother! thanks for you.
Comment by daniel majela — July 13, 2017 #
Thanks. It helped.
Comment by Raghu M — February 27, 2018 #
Thank you very much. Great article.
regards,
Adrian Jung (bluecon)
Comment by bluecon — August 15, 2018 #
Danke, funktioniert prima. Super Tipp!
Comment by lightpen — August 17, 2018 #
Thanks for the tip. Real helpful.
Comment by Jaideep — October 18, 2018 #
The instruction is very helpful. Thank you.
Just wondering if you can search a string in the decrypted text?
Comment by junk1 — July 30, 2021 #